Cisco Intercloud Fabric Release Notes, Release 2.1.2
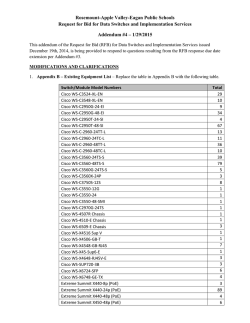
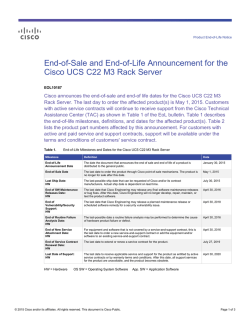
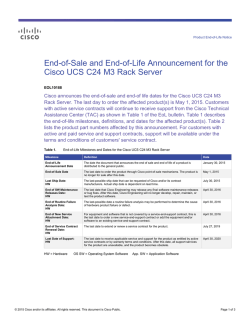
Cisco Intercloud Fabric Release Notes, Release 2.1.2 Cisco Intercloud Fabric Release Notes 2 New and Changed Information 2 Cisco Intercloud Fabric Overview 2 Intercloud Fabric New Features and Enhancements 2 Software Compatibility 3 Supported Cloud Providers 3 System Requirements 4 Scalability Limits 6 Important Notes 6 Prime Network Services Controller Important Notes 7 Open and Resolved Bugs 9 Using the Bug Search Tool 9 Open Bugs 10 Related Documentation for Cisco Intercloud Fabric 11 Documentation Feedback 12 Obtaining Documentation and Submitting a Service Request 12 Revised: January 29, 2015, Cisco Intercloud Fabric Release Notes This document describes the features, limitations, and caveats for the Cisco Intercloud Fabric Release 2.1.2 software. New and Changed Information The following table describes information that has been added or changed since the initial release of this document. Date Revision Location January 29, 2015 Updated system requirements for provider clouds. System Requirements, on page 4 January 14, 2015 Added CSCus50200 to the list of open bugs. Open Bugs, on page 10 January 6, 2015 Updated the operating system versions that are supported for cloud providers. Supported Cloud Providers, on page 3 December 23, 2014 Initial version. — Cisco Intercloud Fabric Overview Cisco Intercloud Fabric provides the architectural foundation for secure hybrid clouds, allowing enterprises to connect the enterprise data center easily and securely to the public cloud as needed and on demand. With a hybrid cloud, enterprises can combine the benefits of public and private clouds. Cisco Intercloud Fabric provides the following benefits: • Provides a single point of management and control for physical and virtual workloads across multiple public clouds • Provides a choice of cloud providers, such as Amazon, Azure, and Dimension Data • Provides highly secure, scalable connectivity to extend private clouds to service provider clouds • Enforces consistent network and workload policies throughout the hybrid cloud • Enables workload mobility to and from service provider clouds for physical and virtual workloads For more information, see Cisco Intercloud Fabric. For information on the Cisco Intercloud Fabric Provider Platform, contact your Cisco representative. Intercloud Fabric New Features and Enhancements This release of Intercloud Fabric contains the following new features and enhancements: • Template sharing across Intercloud Fabric Cloud • Intercloud Fabric license enforcement 2 • Reduced image size for all providers • Improved error handling • Enhanced task-progress reporting functionality • GUI enhancements for simplified infrastructure and private VDC setup • Single-device profile to improve ease of use • Name changes: ◦Cisco Virtual Security Gateway (VSG) is now Intercloud Fabric Firewall. ◦Cisco Cloud Services Router 1000V (CSR 1000V) is now Intercloud Fabric Router. • New APIs Software Compatibility When you deploy Cisco Intercloud Fabric, Cisco Prime Network Services Controller (PNSC) is deployed using the Infrastructure wizard. Similarly, if you choose to deploy services using Cisco Intercloud Fabric, Intercloud Fabric Firewall (VSG) and Intercloud Fabric Router (CSR) are deployed using the Cloud Setup wizard. You do not require a separate license for PNSC or VSG for Cisco Intercloud Fabric. See the Cisco Intercloud Fabric for Business Data sheet for information about ordering. In this release, Cisco Intercloud Fabric is supported only on VMware vSphere. Cisco Nexus 1000V is not a prerequisite for Cisco Intercloud Fabric, but if used, must comply with the minimum version shown in the table below. The following table lists the minimum software versions required for deploying Cisco Intercloud Fabric, Release 2.1.2. Table 1: Software Compatibility Software Minimum Version Required Cisco Prime Network Services Controller (PNSC) 3.4.2 Intercloud Fabric Firewall (VSG) 5.2.(1) VSG (2.1.1) Intercloud Fabric Router (CSR) 3.13.1 Virtual Switch Versions Cisco Nexus 1000V 4.2(1)SV2(2.1) and higher VMware vSphere 5.1 (including update 1) and 5.5 Supported Cloud Providers The following table identifies the cloud providers and operating system versions that are supported in Cisco Intercloud Fabric, Release 2.1.2. 3 Table 2: Supported Cloud Providers Supported Cloud Providers Amazon Web Services (AWS) Supported OS Version • RHEL 6.0 - 6.5: 64-bit versions • CentOS 6.2, 6.3, 6.4, 6.5: 64-bit versions • Windows 2008 R2 SP1 Microsoft Azure • RHEL 6.0 - 6.5: 64-bit versions • CentOS 6.2, 6.3, 6.4, 6.5: 64-bit versions • Windows 2008 R2 SP1 Cisco Hybrid Cloud Bundle — in partnership with Dimension Data • RHEL 6.0 - 6.5: 64-bit versions • Windows 2008 R2 SP1 Note In this release, enabling services such as Intercloud Fabric Firewall (Virtual Security Gateway) and Intercloud Fabric Router (CSR 1000V) is supported only on Amazon Web Services. System Requirements The following tables identify the system requirements for installing Cisco Intercloud Fabric. Table 3: System Requirements for Private Clouds Requirements Description Host One host for hosting Intercloud Fabric components CPUs 64-bit x86 CPU (VT-capable) Memory 32 GB RAM Disk space 500 GB Network interface cards (NICs) 2 (1 GB or 10 GB) VMware ESXi 5.1, 5.5 Intercloud Fabric Director Memory 4 8 GB Requirements Description CPU 4v CPU Disk 100 GB Processor x86 Intel or AMD server with 64-bit processor listed in the VMware compatibility matrix Client Requirements Operating system Microsoft Windows or Apple Mac OS Browser Google Chrome 32.0 or higher Note Flash player We recommend that you use Google Chrome for Intercloud Fabric. Adobe Flash Player plugin 11.9 or higher Intercloud Fabric Extender Memory 2 GB CPU 2 vCPU Disk 4 GB Intercloud Fabric VSM Memory 2 GB CPU 1 vCPU Disk 3 GB Cisco Prime Network Services Controller CPU 4 vCPU Memory 8 GB Disk 220 GB Table 4: System Requirements for Provider Clouds Provider / Model Device vCPU Memory (GB) Disk (GB) r3.xlarge Intercloud Fabric Switch 4 30 20 c3.xlarge Intercloud Fabric Router 4 7.5 8 m1.medium Intercloud Fabric Firewall (VSG) 1 3.75 20 AWS 5 Provider / Model Device vCPU Memory (GB) Disk (GB) A3 Intercloud Fabric Switch 4 7 20 All Other Providers Intercloud Fabric Switch 4 4 20 Azure Note • For optimal performance, we recommend reserving extra system resources for Intercloud Fabric Director above the minimum system requirements listed in the above table. For more information, see the topic "Reserving System Resources" in the Intercloud Fabric Getting Started Guide. • Cisco Intercloud Fabric chooses the VM instance on the provider cloud that most closely matches the VM requirements. Scalability Limits The following table lists the scalability limits for the Cisco Intercloud Fabric components. Table 5: Scalability Limits Cisco Intercloud Fabric Components Scalability Limits Number of VMs per Intercloud Fabric Not to exceed 1000 Number of Intercloud Fabric Cloud per Intercloud Fabric 16 Number of VLANs per Intercloud Fabric Cloud 16 Number of VMs per Intercloud Fabric Cloud 100 Number of vNICs per Intercloud Fabric Cloud 256 Number of Intercloud Fabric Firewalls (VSGs) and Intercloud 2 each Fabric Routers (CSR 1000Vs) Important Notes This section describes the important notes for using Cisco Intercloud Fabric, Release 2.1.2. • When deploying an Intercloud Fabric Cloud by using the Intercloud Fabric wizard, in the Location field, choose a cloud provider location that matches your local time zone to avoid WAN delay and latency. 6 • While cloning an Intercloud Fabric Cloud, you must not migrate the source virtual machine as well as the destination virtual machine as it will impact the cloning operation and any operations carried out on the destination virtual machine after migration. • For the cloud provider Microsoft Azure, you must register the certificate with the Azure portal. • Out-of-band operations are not supported in Intercloud Fabric. If you terminate a virtual machine from the Cloud Provider Portal, the status is not reflected in the Intercloud Fabric GUI. • Trunk ports are not supported in cloud virtual machines. • Trunk ports are not supported in virtual machines that have been migrated to the cloud. • In Microsoft Azure, when you terminate a virtual machine in the cloud, the virtual machine is terminated; however, the storage is not deleted from the image and you will be charged for the virtual machine by the provider. To delete the storage and the image, delete the template used to create the virtual machine using the Intercloud Fabric GUI. • Network Address Translation (NAT) functionality for Intercloud Fabric Router (CSR 1000V) is available only if there is a default VPC in Amazon Web Services (AWS). • During deployment of Intercloud Fabric Router (CSR 1000V) in the cloud, inter-VLAN traffic might stop working between private and cloud virtual machines for VLANs that are not extended to cloud. For private VLANs that are not extended, you must add routing on the data interface configured as the default gateway. If no data interface is configured as default gateway, add one with one of the private VLANs that are not extended, and add routing for the remaining VLANs under that interface. • If the network connectivity between the Intercloud Fabric and the cloud provider is slow, image upload operations, such as migrating a virtual machine, might fail. If the image is not uploaded within 12 hours, the operation will fail and Intercloud Fabric will try to reupload the image. • Some cloud providers require execution of sysprep on the virtual machine image after VM migration. Execution of sysprep leads to certain configuration changes within your virtual machine. These changes include resetting the Windows Administrator password, removing the virtual machine from its associated domain, and other changes. To address these effects of sysprep execution, be aware of the following after migrating the virtual machine to the cloud provider: 1 The Windows password is reset to the name of the virtual machine as entered by you in the VM name field in the Assign VM dialog box. (See the topic "Assigning a Virtual Machine to a Virtual Data Center" in the Intercloud Fabric Getting Started Guide for more information.) If the name of the virtual machine is less than ten characters, the password is reset to the name of the virtual machine appended with the required number of 3's to reach the ten-character limit. 2 If the virtual machine was part of a domain, you must manually readd the virtual machine to the domain after the migration is complete and connectivity to the private network is up. • Before you migrate a virtual machine from the Intercloud Fabric Cloud to the enterprise, make sure that there is sufficient storage capacity in the enterprise for the virtual machine. • Before you migrate a virtual machine from the Intercloud Fabric Cloud to the enterprise, you must add the resource pool to the default computing policy. You can then select the resource pool you added in the Migrate VM Back on Premise window during migration. Prime Network Services Controller Important Notes The following topics provide important information for using Prime Network Services Controller: • No Private Data Center Support in Prime Network Services Controller, on page 8 • Firewall Ports Requiring Access, on page 8 7 • Out-of-Band Operations on Cloud VMs Are Not Supported, on page 8 • Editing Firewall Interfaces, on page 8 • Cloned Linux Virtual Machines, on page 9 • Searching with Special Characters, on page 9 No Private Data Center Support in Prime Network Services Controller Prime Network Services Controller does not support private data center service nodes even though the Cisco Prime Network Services Controller 3.3 User Guide and online help describe how to configure and manage these items. The affected service nodes are ASA 1000V edge firewalls, enterprise CSR 1000V edge routers, enterprise VSG compute firewalls, Citrix NetScaler 1000V load balancers, and Citrix NetScaler VPX load balancers. Also, Prime Network Services Controller does not support integration with Prime Performance Manager even though it is documented in the Cisco Prime Network Services Controller 3.3 User Guide and online help. Firewall Ports Requiring Access If Prime Network Services Controller is protected by a firewall, the following ports on the firewall must be open so that clients can contact Prime Network Services Controller. Port Description 22 TCP 80 HTTP 443 HTTPS 843 Adobe Flash 6644, 6646 TCP, UDP Out-of-Band Operations on Cloud VMs Are Not Supported Out-of-band operations on cloud VMs are not supported. For example, if you terminate a cloud VM from a cloud provider portal, the status is not reflected in Prime Network Services Controller. Editing Firewall Interfaces We recommend that you do not edit the data interfaces of compute or edge firewalls. Changing the data interface via the Prime Network Services Controller GUI will stop communications between the Cisco Nexus 1000V VEM link and the firewall, and thereby stop vPath traffic. If you change the data interfaces of compute or edge firewalls via the Prime Network Services Controller GUI, make the appropriate configuration changes on the Nexus 1000V. 8 Cloned Linux Virtual Machines When Linux virtual machines are cloned, new MAC addresses are assigned. This causes a MAC address mismatch between the VM settings and the Linux Guest OS. If you encounter this situation, the following message is displayed: The Guest OS either does not contain interface configuration for the VM NICs or the interfaces are explictly disabled. For information on how to resolve the MAC address mismatch, see the VMware Knowledge Base. Searching with Special Characters Searching for organization names will not work if the organization names include special characters, such as $. Open and Resolved Bugs The open and resolved bugs for this release are accessible through the Cisco Bug Search Tool. This web-based tool provides you with access to the Cisco bug tracking system, which maintains information about bugs and vulnerabilities in this product and other Cisco hardware and software products. Note You must have a Cisco.com account to log in and access the Cisco Bug Search Tool. If you do not have one, you can register for an account. For more information about the Cisco Bug Search Tool, see the Bug Search Tool Help & FAQ. Using the Bug Search Tool This topic explains how to use the Bug Search Tool to search for a specific bug or to search for all bugs in a release. Procedure Step 1 Step 2 Step 3 Step 4 Go to Cisco Bug Search Tool. In the Log In screen, enter your registered Cisco.com username and password, and then click Log In. The Bug Search page opens. Note If you do not have a Cisco.com username and password, you can register for them at http://tools.cisco.com/RPF/ register/register.do. To search for a specific bug, enter the bug ID in the Search For field and press Enter. To search for bugs in the current release: a) In the Search For field, enter Cisco Intercloud Fabric 2.1.2 and press Enter. (Leave the other fields empty.) b) When the search results are displayed, use the filter tools to find the types of bugs you are looking for. You can search for bugs by status, severity, modified date, and so forth. Tip To export the results to a spreadsheet, click the Export Results to Excel link. 9 Open Bugs The following are descriptions of the open bugs in Cisco Intercloud Fabric, Release 2.1.2. The bug ID links you to the Cisco Bug Search tool. Bug ID Headline CSCuo40162 You cannot change two or more interface service profiles of the Intercloud Fabric Router to the default interface service profile in one transaction in Prime Network Services Controller. CSCup03713 Intercloud Fabric Router (CSR 1000V) goes to failed state if an incorrect NAT rule is applied. CSCuq66672 If you change a tunnel profile in an Intercloud Fabric Cloud, the changes are not displayed if you clone the updated Intercloud Fabric Cloud. CSCuq74832 In the Virtual Accounts window, selecting a Credential Policy is not supported. CSCuq90167 Intercloud Fabric Routers (CSR 1000Vs) enter the Failed-to-apply state if they are configured with a NAT policy source match condition with the attribute Network Port. CSCur53322 The public interface of the Intercloud Fabric Router disappears from the running configuration after you stop or start the Intercloud Fabric Router from Prime Network Services Controller. CSCur64373 In the Infrastructure Setup Wizard (Intercloud > Infrastructure > Setup Wizard), the Datastore for Networking and Placement is shown as empty even though the VMware vCenter was successfully added. CSCur69344 If multiple users concurrently log in to Intercloud Fabric Director as an admin and an end user using different windows of the same browser on the same system and browse Intercloud Fabric Director, Intercloud Fabric Director can give unexpected results. CSCus03598 When migrating public cloud VMs to the private cloud, the first migration to the private cloud succeeds, but subsequent migration attempts fail. This situation occurs when using Intercloud Fabric Provider Platform and the Cisco Hybrid Bundle — in partnership with Dimension Data. CSCus13614 If the connection between Intercloud Fabric and Prime Network Services Controller is reset during Infrastructure setup, the Infrastructure setup fails. CSCus13667 If you migrate a RHEL 6.3 VM from an Amazon cloud to the private cloud, the IP information for the NIC might be lost if the source VM from which the template was created contained incorrect udev rules. CSCus17640 If you start to clone an Intercloud Fabric Cloud and then delete the source Intercloud Fabric Cloud before the creation of the cloned intercloud link is started, the deletion of Intercloud Fabric Cloud is displayed as having failed when it actually succeeds. CSCus18232 Instantiating an Intercloud Fabric Firewall (VSG) can take 30-45 minutes if Prime Network Services Controller is not reachable and the Intercloud Fabric Firewall needs to reregister with Prime Network Services Controller. 10 Bug ID Headline CSCus22740 Occasionally, during the initial installation of an Intercloud Fabric Cloud, the Intercloud Fabric Extender fails to register during the Intercloud Fabric Cloud setup. CSCus22782 The VLAN information does not get deleted when you reboot the Intercloud Fabric Router (CSR 1000V) from the Intercloud Fabric Director or the Prime Network Services Controller. CSCus27812 Creating a Windows 2008 VM fails in the Dimension Data region. CSCus50200 When using Microsoft Azure, creating an Intercloud link fails if no value is specified for the Account Type. Related Documentation for Cisco Intercloud Fabric This section lists the documents used with Cisco Intercloud Fabric and available at the following URL: http://www.cisco.com/c/en/us/support/cloud-systems-management/intercloud-fabric/tsd-products-support-series-home.html General Information Cisco Intercloud Fabric Release Notes Install and Upgrade Cisco Intercloud Fabric Getting Started Guide User Guides Cisco Intercloud Fabric User Guide Cisco Prime Network Services Controller User Guide Configuration Guides Cisco Intercloud Fabric Firewall Configuration Guide Cisco vPath and vServices Reference Guide for Intercloud Fabric Programming Guide Cisco Intercloud Fabric Director REST API Guide Troubleshooting and Alerts Cisco Intercloud Fabric Troubleshooting Guide Cisco Nexus 1000V Documentation Cisco Nexus 1000V for VMware vSphere 11 Cisco Virtual Security Gateway Documentation Cisco Virtual Security Gateway Cisco Prime Network Services Controller Documentation Cisco Prime Network Services Controller Cisco Cloud Services Router Documentation Cisco Cloud Services Router 1000V Documentation Feedback To provide technical feedback on this document, or to report an error or omission, please send your comments to: [email protected]. We appreciate your feedback. Obtaining Documentation and Submitting a Service Request For information on obtaining documentation, using the Cisco Bug Search Tool (BST), submitting a service request, and gathering additional information, see What's New in Cisco Product Documentation, at: http://www.cisco.com/c/en/us/td/docs/general/whatsnew/ whatsnew.html. Subscribe to What's New in Cisco Product Documentation, which lists all new and revised Cisco technical documentation as an RSS feed and delivers content directly to your desktop using a reader application. The RSS feeds are a free service. 12 THE SPECIFICATIONS AND INFORMATION REGARDING THE PRODUCTS IN THIS MANUAL ARE SUBJECT TO CHANGE WITHOUT NOTICE. ALL STATEMENTS, INFORMATION, AND RECOMMENDATIONS IN THIS MANUAL ARE BELIEVED TO BE ACCURATE BUT ARE PRESENTED WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED. USERS MUST TAKE FULL RESPONSIBILITY FOR THEIR APPLICATION OF ANY PRODUCTS. THE SOFTWARE LICENSE AND LIMITED WARRANTY FOR THE ACCOMPANYING PRODUCT ARE SET FORTH IN THE INFORMATION PACKET THAT SHIPPED WITH THE PRODUCT AND ARE INCORPORATED HEREIN BY THIS REFERENCE. IF YOU ARE UNABLE TO LOCATE THE SOFTWARE LICENSE OR LIMITED WARRANTY, CONTACT YOUR CISCO REPRESENTATIVE FOR A COPY. The Cisco implementation of TCP header compression is an adaptation of a program developed by the University of California, Berkeley (UCB) as part of UCB's public domain version of the UNIX operating system. All rights reserved. Copyright © 1981, Regents of the University of California. NOTWITHSTANDING ANY OTHER WARRANTY HEREIN, ALL DOCUMENT FILES AND SOFTWARE OF THESE SUPPLIERS ARE PROVIDED “AS IS" WITH ALL FAULTS. CISCO AND THE ABOVE-NAMED SUPPLIERS DISCLAIM ALL WARRANTIES, EXPRESSED OR IMPLIED, INCLUDING, WITHOUT LIMITATION, THOSE OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT OR ARISING FROM A COURSE OF DEALING, USAGE, OR TRADE PRACTICE. IN NO EVENT SHALL CISCO OR ITS SUPPLIERS BE LIABLE FOR ANY INDIRECT, SPECIAL, CONSEQUENTIAL, OR INCIDENTAL DAMAGES, INCLUDING, WITHOUT LIMITATION, LOST PROFITS OR LOSS OR DAMAGE TO DATA ARISING OUT OF THE USE OR INABILITY TO USE THIS MANUAL, EVEN IF CISCO OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. Any Internet Protocol (IP) addresses and phone numbers used in this document are not intended to be actual addresses and phone numbers. Any examples, command display output, network topology diagrams, and other figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental. Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. and other countries. To view a list of Cisco trademarks, go to this URL: http:// www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1110R) © 2014-2015 Cisco Systems, Inc. All rights reserved. Americas Headquarters Cisco Systems, Inc. San Jose, CA 95134-1706 USA Asia Pacific Headquarters Cisco Systems (USA) Pte. Ltd. Singapore Europe Headquarters Cisco Systems International BV Amsterdam, The Netherlands Cisco has more than 200 offices worldwide. Addresses, phone numbers, and fax numbers are listed on the Cisco Website at www.cisco.com/go/offices.
© Copyright 2026